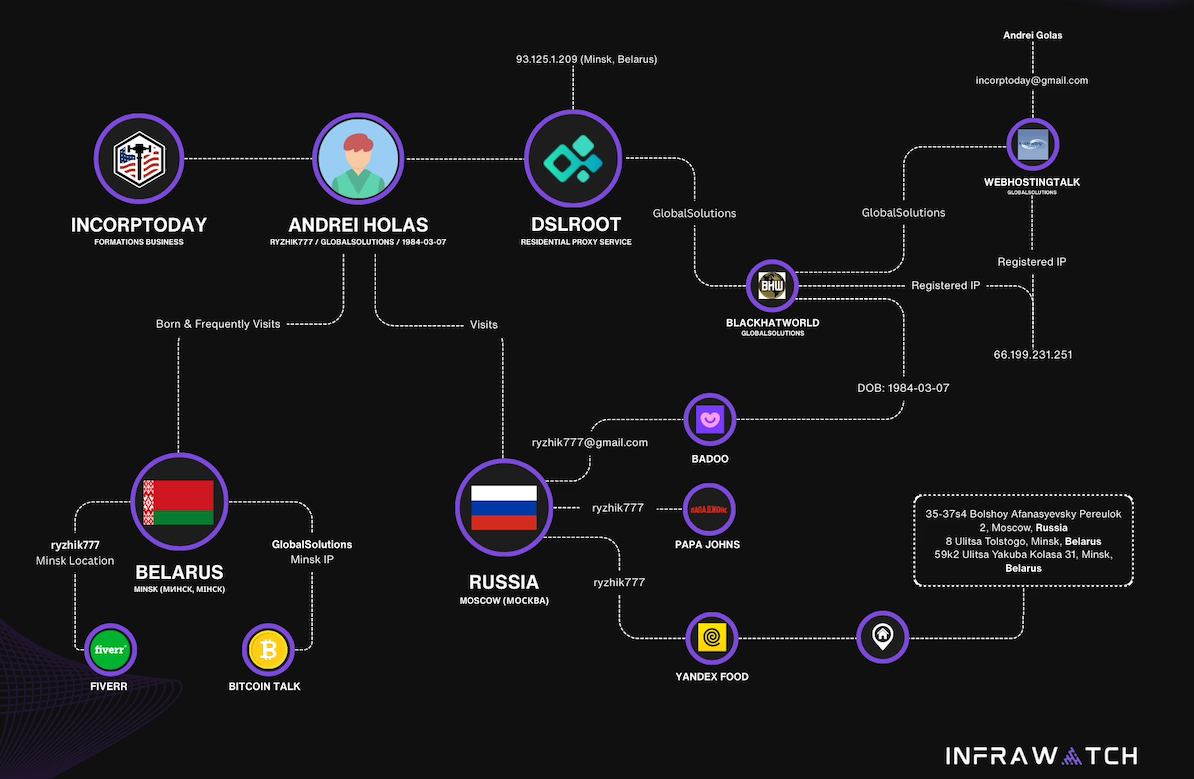
The cybersecurity community recently encountered a peculiar arrangement involving a company named DSLRoot and an individual identifying as an Air National Guard member with top-secret clearance. This individual posted on Reddit, expressing disbelief over a deal where DSLRoot paid $250 per month to utilize the Redditor’s high-speed internet connection in the United States via two laptops. This situation brings to light the operations of “residential proxy” networks, with DSLRoot being identified as one of the oldest in this category, having origins in Russia and Eastern Europe. The core of the issue revolves around the potential for such networks to be exploited, creating what can be termed “legal botnets.”
The analysis of DSLRoot and similar residential proxy networks reveals a complex ecosystem where legitimate-looking services can mask potentially illicit activities. DSLRoot’s business model appears to involve acquiring access to residential internet connections, often through individuals who are compensated for sharing their bandwidth. The company then resells this access to clients who use it for various purposes, including web scraping, market research, and potentially more nefarious activities. The origin of DSLRoot, traced back to Russia and Eastern Europe, is a significant detail, as these regions have historically been associated with sophisticated cybercrime operations. While the source material does not explicitly state that DSLRoot is involved in illegal activities, the nature of residential proxy networks and their potential for misuse warrants careful consideration. The term “legal botnet” itself is an oxymoron, highlighting the dual nature of these services: they operate within a legal framework by compensating individuals for their internet access, yet the aggregated use of these connections can mimic the distributed nature of a botnet, albeit with the consent of the end-user whose connection is being utilized. The Air National Guard member’s post serves as a critical piece of anecdotal evidence, bringing attention to the fact that even individuals with high-level security clearances might be unknowingly participating in such networks. The $250 monthly payment, while seemingly attractive, could be a lure to mask the true intent of the service provider. The cybersecurity community’s reaction underscores the novelty and concern surrounding this practice, as it blurs the lines between legitimate internet sharing and the creation of a distributed network that could be leveraged for malicious purposes without the direct knowledge of the ultimate beneficiaries.
The advantages of using residential proxy networks like DSLRoot, from the perspective of a client, are primarily related to anonymity and the ability to bypass geo-restrictions or IP-based blocking. By routing traffic through a multitude of residential IP addresses, clients can appear as legitimate users from various locations, making their online activities harder to detect and block. This is particularly useful for large-scale data collection from websites that employ anti-scraping measures. The source material implies that DSLRoot has been operating for a considerable time, suggesting a degree of operational success and client demand. However, the significant drawbacks and risks associated with these networks are substantial. The primary concern is the potential for these networks to be used for illegal activities, such as distributed denial-of-service (DDoS) attacks, credential stuffing, or other forms of cybercrime. While the individuals providing their internet access are compensated and may not be aware of the ultimate use of their connection, they could inadvertently become complicit in illegal activities, potentially facing legal repercussions. Furthermore, the security implications for the individuals sharing their internet are also a concern; their network could be exploited for malicious purposes, potentially compromising their own devices or data. The lack of transparency regarding the end-users of these proxy services is a critical weakness, as it allows for the concealment of malicious actors.
Key takeaways from the analysis of DSLRoot and residential proxy networks include:
- DSLRoot is identified as one of the oldest “residential proxy” networks, with origins in Russia and Eastern Europe.
- The company compensates individuals for plugging laptops into their high-speed internet connections, a practice that has raised concerns within the cybersecurity community.
- The arrangement can be seen as creating “legal botnets,” where legitimate residential IP addresses are aggregated and utilized for online activities, potentially masking malicious intent.
- Clients of such services benefit from enhanced anonymity and the ability to bypass IP-based restrictions, facilitating activities like web scraping.
- A significant risk is the potential for these networks to be exploited for illegal cyber activities, with individuals unknowingly becoming conduits for such actions.
- The practice blurs ethical and legal lines, as compensated participants may not fully understand the downstream use of their internet bandwidth.
Educated readers should consider the implications of residential proxy networks for both cybersecurity and personal digital responsibility. It is advisable to remain vigilant about unsolicited offers to share internet bandwidth, especially those offering unusually high compensation. Further research into companies operating in the residential proxy space and their operational transparency is warranted. Understanding the potential for your own internet connection to be leveraged in ways you do not intend is a crucial aspect of modern digital citizenship. The ongoing evolution of these proxy services suggests that this is an area that will continue to present challenges for cybersecurity professionals and regulators alike. Monitoring reports and discussions from cybersecurity experts regarding the misuse of residential IP addresses will be important for staying informed about emerging threats and best practices.
For further context and details on this topic, readers are encouraged to refer to the original article at https://krebsonsecurity.com/2025/08/dslroot-proxies-and-the-threat-of-legal-botnets/.

Leave a Reply