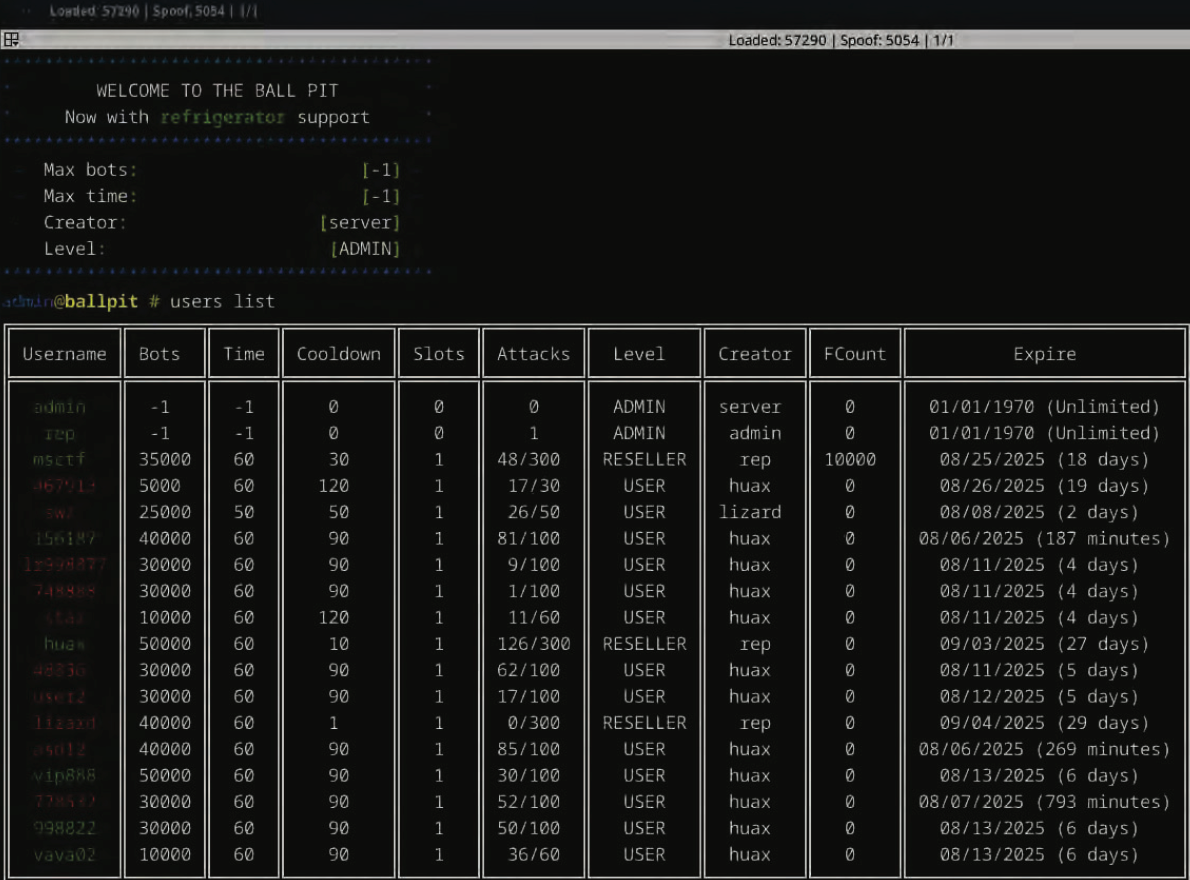
A 22-year-old man from Oregon has been arrested and charged in connection with the operation of “Rapper Bot,” a significant botnet utilized to facilitate distributed denial-of-service (DDoS) attacks. This service is alleged to have been employed for various malicious activities, including a notable DDoS attack in March 2025 that rendered Twitter/X inaccessible. The Justice Department’s assertions indicate that the arrested individual, along with an unidentified accomplice, profited by renting out this botnet infrastructure to individuals engaged in online extortion. A key aspect of their alleged operational strategy involved deliberately avoiding targeting KrebsOnSecurity to evade law enforcement attention, as detailed in the provided source material (https://krebsonsecurity.com/2025/08/oregon-man-charged-in-rapper-bot-ddos-service/).
The core of the Justice Department’s case against the Oregon man centers on his alleged role as an operator of the Rapper Bot botnet. This botnet, described as “massive,” provided the technical capability to launch coordinated DDoS attacks. The analysis of the source material suggests that the service operated on a rental model, making the botnet’s power available to third parties for their own illicit purposes, specifically online extortion. The indictment, as reported, outlines the alleged activities of the suspect and his co-conspirator in managing and monetizing this botnet. The prosecution’s evidence likely involves tracing the infrastructure, communication, and financial transactions associated with the Rapper Bot service. The deliberate exclusion of KrebsOnSecurity from the botnet’s targets is presented as an attempt to remain undetected by law enforcement, implying a level of sophistication and awareness of investigative methods on the part of the alleged operators.
The strengths of the Justice Department’s case, as inferred from the source, lie in the direct accusation of operating a botnet used for criminal activities and the specific mention of a high-profile target like Twitter/X. The alleged business model of renting out the botnet to extortionists provides a clear motive and a framework for understanding the operation’s financial underpinnings. The attempt to avoid detection by not targeting KrebsOnSecurity, while a defensive tactic, also serves as an indicator of the operators’ awareness of potential scrutiny. The weakness, or rather the area requiring further substantiation through the legal process, would be the definitive proof of the suspect’s direct involvement and control over the botnet’s operations and the extent of the co-conspirator’s role. The source material focuses on the charges and the alleged activities, and the full scope of evidence will be revealed during any subsequent legal proceedings.
The most critical takeaways from the provided information are:
- A 22-year-old Oregon man has been charged in connection with the Rapper Bot botnet.
- Rapper Bot is alleged to have been used to power DDoS attacks, including one that impacted Twitter/X in March 2025.
- The Justice Department asserts the botnet was rented out to online extortionists.
- The suspect and an alleged co-conspirator are accused of attempting to evade law enforcement.
- A specific tactic mentioned for evasion was ensuring the botnet was never pointed at KrebsOnSecurity.
- The case highlights the ongoing threat posed by botnets and their use in cybercrime and extortion.
An educated reader should consider monitoring the legal proceedings related to this case to understand the evidence presented and the legal arguments employed by both the prosecution and the defense. Further analysis of how law enforcement agencies identify and dismantle such botnets, and the challenges involved in prosecuting individuals operating them, would also be beneficial. Observing the broader implications for cybersecurity and the ongoing efforts to combat DDoS-for-hire services is also a relevant next step.
The Justice Department has charged a 22-year-old Oregon man in connection with the operation of “Rapper Bot,” a botnet used for distributed denial-of-service (DDoS) attacks (https://krebsonsecurity.com/2025/08/oregon-man-charged-in-rapper-bot-ddos-service/). This botnet is alleged to have been instrumental in a March 2025 DDoS attack that disrupted Twitter/X. The suspect and an unidentified co-conspirator are accused of renting out the botnet to online extortionists. Their alleged strategy to avoid detection included ensuring the botnet was never directed at KrebsOnSecurity.

Leave a Reply